






























Every time someone picks up a mouse, they make a choice to either strengthen or lessen our security posture.
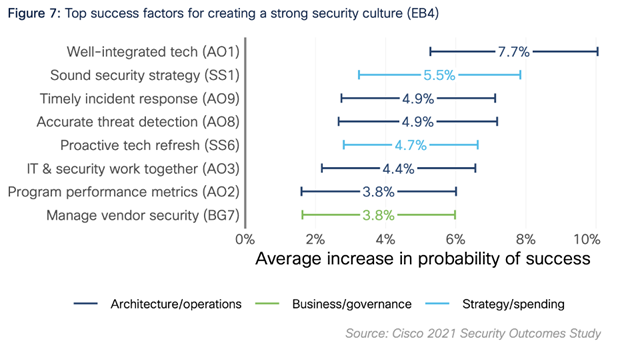
The security team can impact these choices through culture. For a long time, however, it was difficult to know what had to be present to create and manage security culture. The recent Cisco Security Outcomes Study finally shed some light on these factors.
Culture is built one action at a time. Since the rise of BYOD and consumerization of IT, people in the workforce have a choice. They can use the organization's technology, or they can go elsewhere. They can opt into the controls, or they can work around security. Actions become habits, habits become behavior, and behavior quickly spreads. The wrong bit of friction, at the wrong time, for the wrong person, can lead entire teams to turn elsewhere for IT services. Constrained users get creative, and creative people are a security concern.
Savvy security leaders are constantly on the hunt for ways to improve usability and user adoption. They partner with IT to ensure the workforce has access to the best available technology. Moreover, leaders work to ensure that security is well integrated, minimizing the steps and choices a person must take to complete their work. In part, I believe that accounts for proactive tech refresh (SS6) and well-integrated tech (AO1) being such contributing factors in security culture.
It is less about getting the latest and greatest, and more about using refreshes as an opportunity to simplify the user experience and, thereby, create the conditions for security culture.
Access the fullCisco 2021 Security Outcomes Study
Preventing security incidents requires identifying what could go wrong, and early detection when things do go wrong. A typical organization may have 20 IT professionals for every security professional, and for every security professional there may be 1,000 employees. Enrolling IT and the broader workforce in detecting and reporting malware, phishing attempts, and other warning signs is crucial to preventing incidents. The data clearly confirms the correlation between response and culture (AO9).
Of course, such reporting must be high fidelity in order to not contribute to alert fatigue. The higher the number of alarms, the greater the percentage of false positives, the more likely a security analyst is to become desensitized and to ignore the alerts. It is accurate threat detection (AO8) which allows the security team to act on signals, which in a culture with security awareness, includes reports from the workforce.
Culture spans the gap between awareness and action. As expected, having security awareness training (BG4) corresponds with creating a security culture. It would be interesting to peel this back and see what form training takes. We've all seen poorly done training, the annual ritual of mindlessly clicking next on the presentations covering security and compliance. Some of the better training programs favor gamification and feature shorter lessons. We simply don't have the data on how the respondents are organizing their training.
Training is the starting point. We've seen how hard it is to get people to act on awareness, from using seatbelts to stopping texting while driving, from stopping smoking to eating better. Cyber security is no different. Behavior economics has spent decades teasing out the barriers to action, and the tactics for getting people there. Two these tactics are tying behaviors to a person's identity and making it a personal routine. Culture is the beliefs and the behaviors of people in our organizations.
Culture is built one conversation at a time. Every interaction is an opportunity to communicate and reinforce secure behaviors. When security operations personnel work effectively and closely with the organization's IT operations and development teams, this provides a cadence for having these conversations. Every plan, every change, every configuration, offers an opportunity to build and bundle security into the infrastructure. We see this in the data (AO3).
Moving up the stack, purchasing software and services provides another cadence for security conversations. Auditing an organization's vendors strengthens the efficacy of controls along the supply chain. Audits also provide an object lesson that's independent of the organization itself, and therefore psychologically feels safer to the employees seeing the faults in others. Managing vendor security (BG7) is a platform for regularly and consistently explaining the security standards to procurement and those with purchasing authority.
From the report: "You can't just impose security on the organization; it must be built into the fabric of the infrastructure and organization itself to really make a difference. Good collaboration among technical teams is essential to that goal."
Culture is built one measure at a time. Now every security tool has metrics and dashboards. Most every security program has metrics. Some have key performance indicators (KPIs) and key risk indicators (KRIs). But while these are useful in driving operational excellence and managing risk, such measures don't easily translate into culture change. We need feedback on the efficacy of any given control. We need metrics that surface work arounds, work hacks, and security policy violations. These are signs that the workforce is struggling to meet our security objectives, enabling the team to better redesign the controls and adjust the process.
What are the right things to measure? Program performance metrics (AO2) which identify areas of friction.
Security culture is above the security poverty line. Security teams need the financial budget to successfully cover the fundamentals. They also need sufficient personnel. Teams focused on firefighting are not well-positioned for building relationships and developing empathy needed for culture change. On a one-on-one basis, an over-worked and burned-out security analyst is the last person you want as an advocate. Don't put a frustrated employee with a frustrated security professional and expect positive change. Security culture requires capacity, and we see this reflected in the data as a strong correlation with budget and staffing (SS2, SS3).
Do you want to kill the security culture? Don't fund the program (SS2). Don't hire enough people for security roles (SS3). Don't train your people (SS4).
For a full listing of all security outcomes, please see
Appendix B of the Security Outcomes Study
You might expect excluding the executive team would be another way to kill culture. Surprisingly, security being important to execs (BG2) wasn't correlated with security culture. That top-down approach, so often advocated for by security consultants and pundits alike, didn't make the cut. If the choice is getting executives on-board with security's priorities, or getting security's priorities aligned with the executives vision, take the latter approach. I was more surprised that the bottom-up approach also didn't make the cut. I've run programs where culture was built one line of code at a time and built one patch at a time. I had expected a stronger showing for vulnerability remediation deadlines (AO5) and secure development (AO6).
Additionally, given the objectives of enabling the workforce while disabling the criminals? Security leaders need to understand the business and security's role (BG1). We also must understand how threats move through the environment, in part, by learning from prior incidents (AO11). That neither of these were correlated likely speaks to the understanding coming from informal or ad hoc processes.
Creating and shaping a security culture requires a focus on usability, services, accurate alerting, awareness, and well-integrated change processes. Culture management needs time and attention, alongside staples like asset management or vulnerability management, in the overall security strategy. The Cisco Security Outcomes Study states "the strategy-culture correlation is worth calling out specifically. This is the only outcome in the 'Enabling the Business' category for which having a sound security strategy significantly increases the probability of success. That may seem odd, but consider that many a frustrated employee has asked something to the effect of 'why do we have to go through all of this?' in response to new security policies. A good strategy eases that frustration by getting everyone on the same page."
 Etiquetas calientes:
Cisco Security Outcomes Report
security awareness
security culture
Etiquetas calientes:
Cisco Security Outcomes Report
security awareness
security culture