






























Cisco is committed to protecting customers by sharing critical security-related information in different formats. Guided by customer feedback, Cisco's Product Security Incident Response Team (PSIRT) is seeking ways to improve how we communicate information about Cisco product vulnerabilities to our Customers and Partners. As John Stewart mentioned on his blog post, the Cisco PSIRT has launched a new and improved security vulnerability disclosure format. The new Cisco Security Advisories can be accessed at http://www.cisco.com/go/psirt and at http://cisco.com/security
The intent is to make it easier for Customers and Partners to access information about all security vulnerabilities in Cisco products. Each vulnerability disclosed through our new security advisories are assigned a Common Vulnerability and Exposures (CVE) identifier to aid in identification. Additionally, Cisco will continue to assess all vulnerabilities using the Common Vulnerability Scoring System (CVSS). Check out the sites for CVE, CVSS, and this CVSS scoring calculator if these terms are relatively new to you or you simply need a refresher.
In the past, Cisco Security Advisories addressed critical and high severity security vulnerabilities, and Cisco Security Alerts documented low and medium severity security vulnerabilities that directly involved Cisco products. The new Cisco Security Advisory will replace the existing security advisories and alerts, addressing all security vulnerabilities of all severities.
Cisco has introduced a simplified way to categorize security vulnerabilities called the Security Impact Rating (SIR). The following are the vulnerability SIR classifications:
| Security Impact Rating | CVSS Score |
|---|---|
| Critical | 9.0 -10.0 |
| High | 7.0 -8.9 |
| Medium | 4.0 -6.9 |
| Low | 3.9 or below |
Note: Cisco reserves the right to deviate from this simple mapping on an exception basis in the event that there are additional factors not properly captured in the CVSS score. Security vulnerabilities that have a low security impact rating will continue to be addressed via Cisco bug Release Note Enclosures (RNEs) available in the Cisco Bug Search Tool.
The following figure shows the new Cisco Security Advisory Security Impact Rating field.
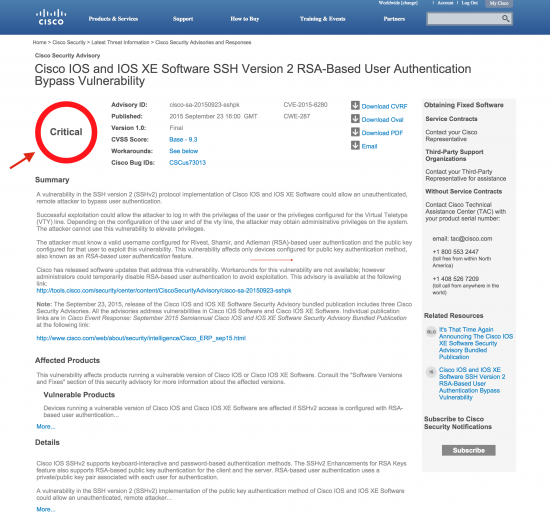 Cisco Security Advisory -Security Impact Rating
Cisco Security Advisory -Security Impact Rating
Cisco PSIRT enhanced the look and feel of the new Cisco Security Advisories based on direct customer feedback. Cisco Security Advisories are often updated based on new information about a given vulnerability investigation. Cisco PSIRT made improvements to each section of the security advisory and incorporated features that make it easier and more apparent for customers when security advisories are updated.
The Cisco Security Advisory listing page has also been improved to allow customers to navigate and search all security publications.
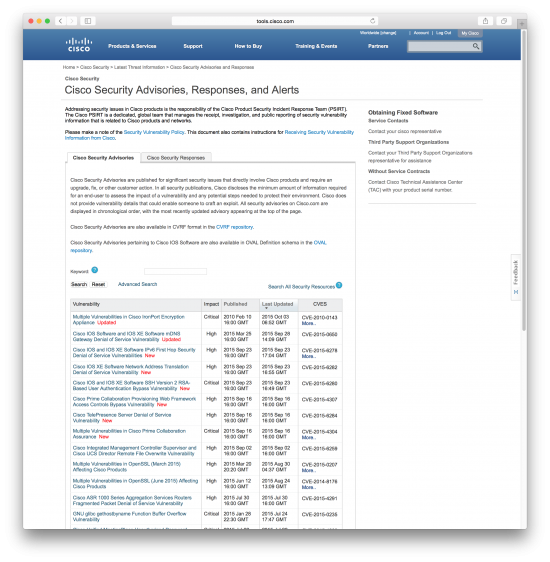 Cisco PSIRT Security Advisories
Cisco PSIRT Security AdvisoriesBy default security advisories that address critical and high severity security vulnerabilities are displayed. Cisco has also enhanced the advanced search to include the new fields and to filter results based on the security impact rating, the CVSS score, publication dates, affected products, CVE IDs, Cisco Bug IDs, and other relevant keywords, as shown below:
 Cisco Security Advisories Advanced Search
Cisco Security Advisories Advanced Search
Cisco PSIRT drives and follows open, global standards and makes decisions to develop and implement new technologies based on customers' current and anticipated requirements. These new Cisco Security Advisories are also available in Common Vulnerability Reporting Framework (CVRF) format. CVRF is a security automation standard intended to make your life easier by offering a common language to exchange security vulnerability advisories.
Cisco Security Advisories in CVRF format can be accessed from the Cisco CVRF repository at:
http://tools.cisco.com/security/center/cvrfListing.x
You can essentially create your own advisory and/or pick the sections of security advisories that are more relevant to you by parsing each CVRF file.
A Python library and CLI tool (cvrfparse) for extracting data out of a CVRF document is available at GitHub.
You can also installcvrfparsefrom source or by using pip:
pip install cvrfparse
The following is a quick reference to cvrfparse's help:
omar@server1:~$cvrfparse --helpusage: cvrfparse [-h] -f FILE[--cvrf [{all,DocumentTitle,DocumentType,DocumentPublisher,DocumentTracking,DocumentNotes,DocumentDistribution,AggregateSeverity,DocumentReferences,Acknowledgments} ...]][--vuln [{all,Title,ID,Notes,DiscoveryDate,ReleaseDate,Involvements,CVE,CWE,ProductStatuses,Threats,CVSSScoreSets,Remediations,References,Acknowledgments} ...]][--prod [{all,Branch,FullProductName,Relationship,ProductGroups} ...]][-c] [-s] [-V] [-S SCHEMA] [-C CATALOG] [-v]Validate/parse a CVRF 1.1 document and emit user-specified bits.optional arguments:-h, --help show this help message and exit-f FILE, --file FILE candidate CVRF 1.1 XML file--cvrf [{all,DocumentTitle,DocumentType,DocumentPublisher,DocumentTracking,DocumentNotes,DocumentDistribution,AggregateSeverity,DocumentReferences,Acknowledgments} ...]emit CVRF elements, use "all" to glob all CVRFelements.--vuln [{all,Title,ID,Notes,DiscoveryDate,ReleaseDate,Involvements,CVE,CWE,ProductStatuses,Threats,CVSSScoreSets,Remediations,References,Acknowledgments} ...]emit Vulnerability elements, use "all" to glob allVulnerability elements.--prod [{all,Branch,FullProductName,Relationship,ProductGroups} ...]emit ProductTree elements, use "all" to glob allProductTree elements.-c, --collate collate all of the Vulnerability elements by ordinalinto separate files-s, --strip-ns strip namespace header from element tags beforeprinting-V, --validate validate the CVRF document-S SCHEMA, --schema SCHEMAspecify local alternative for cvrf.xsd-C CATALOG, --catalog CATALOGspecify location for catalog.xml (default is./cvrfparse/schemata/catalog.xml)-v, --version show program's version number and exit
Cisco has added a new RSS Feed for customers to be able to access and subscribe to new security advisories in CVRF format. The CVRF RSS feed can be accessed at:
http://tools.cisco.com/security/center/cvrf_20.xml
Note: You can also download all Cisco Security Advisories that are in CVRF format from Cisco's CVRF Repository.
Cisco PSIRT continues to publish Open Vulnerability and Assessment Language (OVAL) definitions in Cisco IOS security advisories. OVAL speeds up information exchange and processing of such security-related information. Using OVAL security administrators and other users can accelerate the process of detecting software vulnerabilities in Cisco IOS Software. OVAL content (often called "definitions") can be downloaded directly from Cisco IOS security advisories. Each Cisco IOS security advisory includes a link to the corresponding OVAL definition(s). You can also download OVAL definitions from Cisco's OVAL Repository.
Cisco has added a new RSS feed for customers to be able to download and subscribe to new OVAL definitions for Cisco IOS Software vulnerabilities. The OVAL RSS feed can be accessed at:
http://tools.cisco.com/security/center/oval_20.xml
For more information about OVAL please refer to my earlier blog posts and webcasts:
Cisco's Security Vulnerability Policy provides detailed information about the different ways that customers can receive security vulnerability disclosures from Cisco.
Check out Cisco's Security Vulnerability Policy for more detailed information about how to receive threat, vulnerability, and mitigation information, and the overall vulnerability management process.
Cisco PSIRT will continue to adapt to enable our customers to assess and mitigate any risks in their networks quickly. Our mission is to do the right thing quickly, and to keep our customers protected.
Our goal in introducing this new security vulnerability disclosure document format is to better inform customers about security vulnerabilities in a consistent and transparent way. We want to hear from you if you have questions or feedback that enables us to help you keep pace with that continuous risk mitigation cycle.
The following video summarizes these enhancements:
 Etiquetas calientes:
security vulnerabilities
psirt
security advisories
Cisco PSIRT
cvrf
vulnerability management
security automation
vulnerability disclosure
Etiquetas calientes:
security vulnerabilities
psirt
security advisories
Cisco PSIRT
cvrf
vulnerability management
security automation
vulnerability disclosure