






























Cisco is announcing another important strategic partner to its list of ACI-compliant vendors with the addition of the Check Point Next Generation Security Gateway to the ecosystem. A couple months ago I wrote about the inherent security architecture in ACI (Security for an Application Centric World), and now the Check Point solutions fit right into that framework as an alternative to Cisco security solutions. Essentially, this means that the ACI controller, APIC, can now configure the application network to include the insertion and provisioning of Check Point virtual and physical security gateways as it does other Layer 4-7 application services and security appliances. The availability of the Check Point solutions will offer customers greater choice and flexibility while underscoring the open, multi-vendor approach of ACI.
[Note: Check Point will be participating in our upcoming ACI Webcast event: "Is Your Data Center Ready for the Application Economy", January 13, 2015, 9 AM PT, Noon ET, featuring ACI customers and several other key ACI technology partners. Register here.]
In scalable, multitenant cloud environments with flexible resource placement, almost every workload must be secured from every other workload, with detailed security policies enabled between workloads in an application network: a concept called micro-segmentation. This level of security policy detail can become tedious to manage on an application-by-application basis. It also can potentially restrict workload mobility and the ways that applications can be deployed in the cloud.
Cisco ACI policies abstract the network, devices, and services into a hierarchical, logical object model. In this model, administrators specify the Layer 4 through Layer 7 services (firewalls, load balancers, etc.) that are applied, the kind of traffic to which they are applied, and the traffic that is permitted. These services can be chained together and are presented to application developers as a single object with simple input and output. Connection of application-tier objects and server objects creates an application network profile (ANP). When this ANP is applied to the network, the devices are told to configure themselves to support it. Tier objects can be groups of hundreds of servers, or just one device; the same policies are applied to all the objects in a single configuration step (see below).
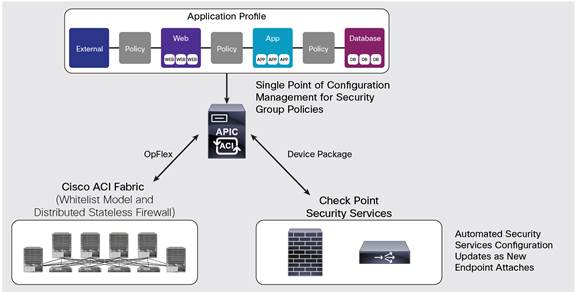 The Application Profile Defines Security and Application Policies for Application Networks, and Cisco APIC Manages and Provisions Security Resources in the Fabric, Such as a Check Point Firewall, with the Right Policies for Each Application, at the Right Location
The Application Profile Defines Security and Application Policies for Application Networks, and Cisco APIC Manages and Provisions Security Resources in the Fabric, Such as a Check Point Firewall, with the Right Policies for Each Application, at the Right LocationThe integration with Check Point Next Generation Security Gateway provides automated security provisioning and a full range of security protections and threat-prevention capabilities in a highly dynamic and agile Cisco ACI environment. Check Point Security Gateways can be deployed as physical or virtual solutions and address today's ever-changing threat landscape with a modular and dynamic security architecture.
Automated Next-Generation Security with Check Point
Check Point Next Generation Security Gateways provide advanced protection, including intrusion prevention system (IPS), application control, URL filtering, data protection, antivirus, anti-bot, and threat prevention capabilities.
The combination of Check Point advanced security and Cisco ACI creates a secure and agile data center environment with many advantages for customers:
Together, Cisco and Check Point provide a powerful security solution incorporated into the leading application policy and infrastructure automation platform: Cisco ACI.
For more information: ACI Check Point Solution Brief
 Etiquetas calientes:
#seguridad
Cisco ACI
Cisco Application Centric Infrastructure (ACI)
IPS
APIC
En los países bajos
Check Point
Etiquetas calientes:
#seguridad
Cisco ACI
Cisco Application Centric Infrastructure (ACI)
IPS
APIC
En los países bajos
Check Point