






























According to research from the Enterprise Strategy Group,87%of organizations use Network Traffic Analysis (NTA) tools for threat detection and response today, and43%say that NTA is a "first line of defense" in case of an attack. The increasing IT complexity is one of the main factors in the adoption of NTA tools -growing infrastructure, rise in hybrid and multi cloud deployments, employees accessing the network from any device and any location, and large number of smart devices (IoT/OT) connecting to the network. At the same time, the attack landscape has evolved as well -use of stolen credentials, threats hiding in encrypted traffic, rise in nation-state attacks, and more.
Perhaps that's why there are so many NTA vendors out there today, trying to catch the attention of security practitioners, carrying their "AI and ML" billboards.
Cisco offers an NTA solution as well, but it wasn't born yesterday. Cisco Stealthwatch has been in the market more than 17 years. And here are some things that make it the market leading NTA solution:
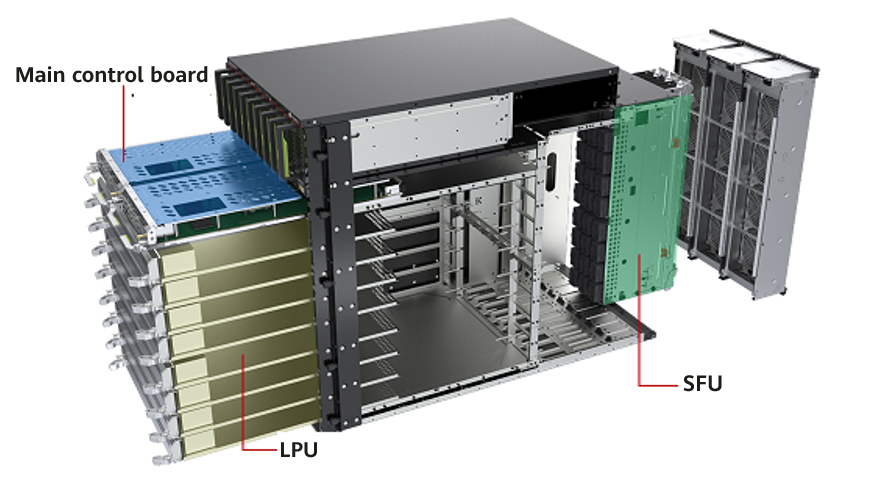
Stealthwatch has always relied on network meta data such as NetFlow to feed into its analytics. Now, some vendors claim that this way of ingesting telemetry doesn't give the complete picture and has limitations. It's because they rely on deploying a large number of sensors and probes in the network to capture data. If I were cynical, I'd say the vendors who take this position want you to buy more probes and increase your workload!
We realized very early on that as the network grows exponentially, it's very difficult (and expensive) to deploy sensors everywhere. And this approach leaves you with a lot of blind spots. That's why we offer an agentless deployment to customers using built in functionality in your network devices. And unlike competitive claims, Stealthwatch doesn't just rely on NetFlow. For example, it gets user contextual data from Cisco Identity Services Engine (ISE) and also ingests proxy, web, and endpoint data to provide comprehensive visibility. If you do need to investigate the payload, Stealthwatch integrates with major packet capture solutions so you can selectively analyze the malicious traffic pinpointed by Stealthwatch.

Visibility is great, but can be dangerous when it begins to overwhelm your security team. The key is effective analytics to reduce that massive dataset to a few actionable alerts. Stealthwatch uses close to 100 different behavioral models to analyze the telemetry and identify anomalies. These anomalies are further reduced to high-level alerts mapped to the kill-chain such as reconnaissance, command-and-control, data exfiltration and others. Stealthwatch also employs machine learning that uses global threat intelligence powered by Cisco Talos and techniques like supervised and unsupervised learning, statistical modeling, rule mining... I could go on. But I want to talk about the outcomes of analytics within the solution:

As organizations increasingly adopt the cloud, they need to ensure that their security controls extend to the cloud as well. Stealthwatch is theonlynetwork traffic analysis solution that can provide truly cloud-native visibility across all major cloud providers like Amazon Web Services (AWS), Microsoft Azure and Google Cloud Platform (GCP). And again, the deployment is agentless without the need to install multiple sensors across the infrastructure. With a single solution, you get visibility across the entire network infrastructure, on-premises to the cloud.
We have been working on integrating Stealthwatch analytics into our security platform that spans the network, endpoint, applications and cloud. Most recently, we have integrated Stealthwatch with Cisco Threat Response. Stealthwatch sends alerts directly to Cisco Threat Response's Incident Manager feature, allowing users to see those alerts alongside prioritized security alerts from other products such as Firepower devices. These incidents can then be investigated with additional context from your other threat response-enabled technologies, all in one console, with one click. This lowers the time required to triage and response to these alarms.
Stealthwatch is also integrated with firewall through the Cisco Defense Orchestrator for threat detection and effective policy management.
Customers, big and small, love and trust Stealthwatch. We count 15 of top 20 US banks, and 14 of top 20 global healthcare companies among our customers. If you would like to try the solution, you can sign up for a free 2-week Stealthwatch visibility assessment at: https://www.cisco.com/go/free-visibility-assessment
Joining us at Cisco Live, Barcelona this week? Here's a guide to all the activities and key sessions related to Stealthwatch at the event or come check out a Stealthwatch demo within the Security area at World of Solutions.
Notes
 Etiquetas calientes:
destacado
#seguridad
incident response
Cisco Stealthwatch
threat detection
security analytics
network visibility
Network Traffic Analysis
Etiquetas calientes:
destacado
#seguridad
incident response
Cisco Stealthwatch
threat detection
security analytics
network visibility
Network Traffic Analysis