






























Leaders at most modern organizations would readily agree that data is critical to today's digital-first businesses. Maybe that's why there are so many metaphors about data with comparisons to oil and currency-it's even described as a lifeblood.
However, the most useful metaphor of all might be seeing data as a key. One that unlocks insights businesses can use to improve customer experience, reduce sales friction, and promote brand loyalty in a hypercompetitive landscape.
Data is so vital, you might think that the adoption of technologies and processes that can help protect, monitor, and detect possible threats-and also be able to recover it from catastrophic events-would be a priority. But according to the latest Cisco Cybersecurity Readiness Index, many companies believe they are falling woefully short of the mark. Consider these stats:
To help our customers build and deploy a robust and secure infrastructure, Cisco and NetApp partnered to develop the FlexPod cybersecure architecture toprotect apps and data from unauthorized access,detect threats early to keep data safe, andrecover data quickly to reduce downtime. Existing FlexPod customers can use this reference architecture to strengthen the security of their FlexPod infrastructures. New FlexPod customers can deploy a more secure solution immediately.
This is the latest achievement that builds on the decade-plus success of Cisco and NetApp delivering compelling innovations for converged infrastructure. This is a validated approach (see below) for deploying tightly integrated compute, networking, storage, and management technologies from Cisco?and NetApp for hybrid and multicloud environments.
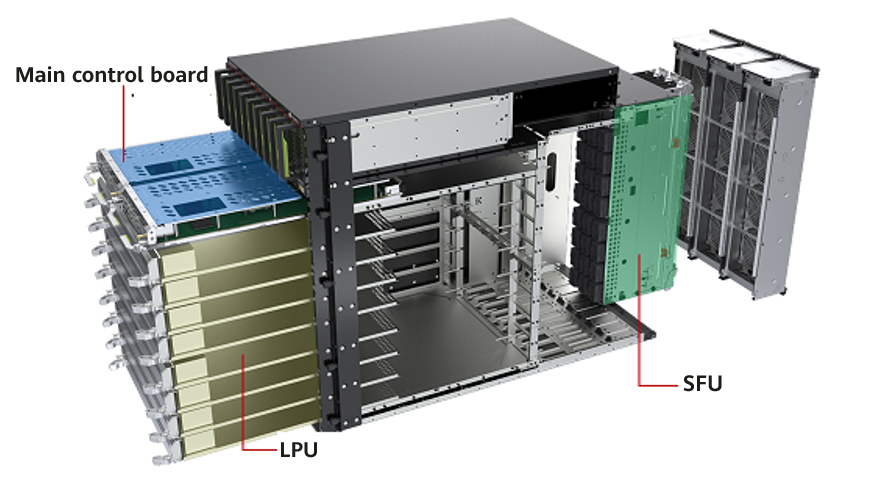
The latest generation of FlexPod is powered by Cisco Unified Computing System (UCS) servers, including the award-winning Cisco UCS X-Series Modular System. The server is managed by Cisco Intersight, which enables IT leaders to easily adapt to the unpredictable needs of modern applications. Combined with NetApp innovations, the FlexPod cybersecure architecture empowers organizations with a strong foundation to maintain the integrity, confidentiality, and availability of their apps and data, ensuring long-term success and resilience in an ever-changing cybersecurity landscape. This proactive approach is further defined by the three cybersecurity pillars of protect, detect, and recover. Here is a brief technical overview:
Applies a?holistic approach to safeguarding?systems, management, data,?and applications via a zero-trust model and architecture. This includes:
Quickly detects, analyzes, and responds to threats, preventing loss and corruption of data via:
Swiftly addresses data protection and recovery in the unlikely event of data breaches and ransomware attacks. User access is quickly blocked upon detecting anomalies, with detailed forensic analysis conducted for future prevention. With policy-based server profiles and data recovery capabilities, FlexPod can restore an environment in minutes to ensure a fast resumption of operations, mitigating the cost of downtime through:
We are diligently working on our latest Cisco Validated Design (CVD), which will show customers how to confidently deploy a FlexPod cybersecure architecture for their specific environments. We stand behind every FlexPod solution with our experience, resources, and technical expertise to deliver full solution support to our customers. We are excited to be incorporating many technical design elements into this CVD, such as the following:
Enables segmentation by tenants (such as application tiers, business units, and managed services) through virtual routing and forwarding (VRF) and virtual LAN concepts within Cisco Nexus switches and Cisco Unified Computing System (UCS) servers-and further protection using Cisco Secure Firewall. The goal is to provide better control and protection of external ("north-south") traffic among tenants.
For additional protection of internal lateral traffic within a data center ("east-west" traffic), the CVD will leverage workload security through microsegmentation, proactive identification of security incidents using behavior analysis, and reduction of the attack surface by identifying software-related vulnerabilities.
Addressing the concept that you can't protect what you can't see, the CVD will use analytical tools and concepts like NetFlow and logs at various points in the network to create a baseline to detect and root out anomalous actions.
Malicious security attacks via ransomware already cost companies billions of dollars a year to recover their data. Cisco and NetApp are planning to integrate our respective ransomware protection capabilities, which will be available through a joint external data representation (XDR) solution.
More information about the FlexPod cybersecurity architecture will be available at the NetApp INSIGHT 2023 event in Las Vegas. Featured sessions include:
We hope to see you there.
Read more about FlexPod and Cisco at NetApp INSIGHT
 Etiquetas calientes:
Seguridad de red
FlexPod
data security
network infrastructure
Etiquetas calientes:
Seguridad de red
FlexPod
data security
network infrastructure