






























This post was authored byArmin Pelkmann and Earl Carter.
Talos Security Intelligence and Research Group noticed a reappearance of several Dridex email campaigns, starting last week and continuing into this week as well. Dridex is in a nutshell, malware designed to steal your financial account information. The attack attempts to get the user to install the malicious software on their system through an until lately, rarely exploited attack vector: Microsoft Office Macros. Recently, we noticed a resurgence of macro abuse. If macros are not enabled, social engineering techniques are utilized to try to get the user to enable them. Once the malware is installed on the system, it is designed to steal your online banking credentials when you access your banking site from an infected system.
Talos analyzed three separate campaigns in the last days, all distinguishable from their subject lines.
The first campaign with the subject line "Industrial Invoices" appeared on December 4th for roughly 2 hours. An interesting fact is that a similar campaign using the same subject line was already used on November 13th when it lasted for 7 hours before going dormant.

This campaign attempted used a malicious word document attached to the email. The mail message was similar to:
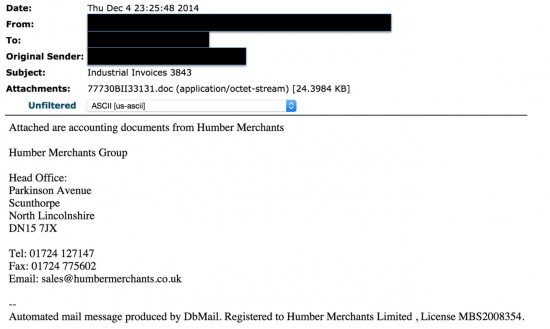
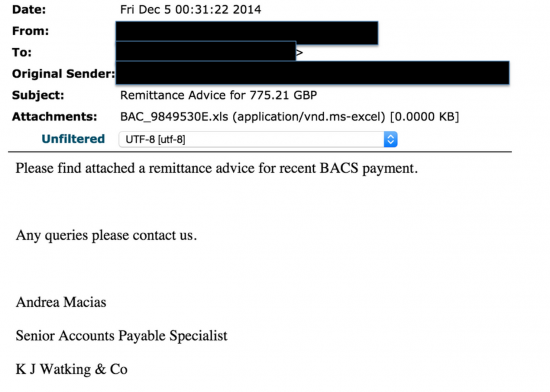
Another campaign also appeared on December 4th using Subject lines like "Remittance Advice for 907.62 GBP" in which the numeric value varied from message to message. This campaign lasted for approximately 2.5 hours.
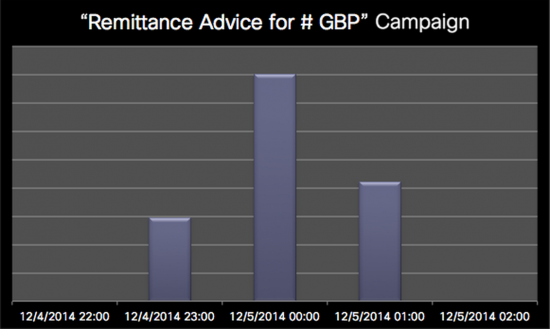
Similar to the previous campaign it also emailed users with a malicious attachment, but in this case, the malicious payload was an Excel spreadsheet instead of a Word document. The goal was still to install the malware through macros.
Finally, on December 7th, another campaign appeared using the subject line "INVOICE 224245 from Power EC Ltd". This campaign lasted for the longest time in that it was active for about 9 hours. This is also a repeat of a similar campaign that occurred on November 12th and lasted for 6 hours.

This campaign had the simplest message with no randomization neither in the subject line nor the body, and this time the attachment again is a Microsoft Word document.

Summary
Dridex seems to be very persistent attack. Some of the attacks above were even used multiple times. It is interesting to see that the attackers are recycling their attacks, which might indicate, that the tool they are using has limited randomization options. One indicator for this is the very limited variation in subject lines and email bodies, which makes detection easier.
Whereas the variation in how many different campaigns are used to target a large amount of different companies (mainly from the financial sector). Despite the very short attack-time-windows our sensors picked up very large amounts of these malicious messages, which suggests that the Dridex network of infected systems sending spam is very large.
Due to the swift execution of those attacks a multi layered defense is extremely important. Reputation systems will most likely miss the first few seconds to minutes of an attack. The very first messages can be most efficiently get stopped by content filters and anti-malware engines.
Snort Rules: 32675-32678
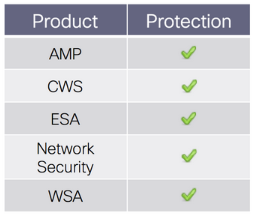
Advanced Malware Protection (AMP) detects the malware used in this campaign.
CWS or WSA web scanning prevents access to malicious websites and detects malware used in these attacks.
The Network Security protection of IPS and NGFW have up-to-date signatures to detect malicious network activity by threat actors.
The ESA is capable of blocking the messages used in this campaign.
 Etiquetas calientes:
#seguridad
Microsoft Microsoft Microsoft Microsoft Microsoft
Cisco Talos
Talos
malware
spam
Dridex
financial
Excel
Etiquetas calientes:
#seguridad
Microsoft Microsoft Microsoft Microsoft Microsoft
Cisco Talos
Talos
malware
spam
Dridex
financial
Excel